Technologies for Conlan Access Control
Reader Communications & Technologies
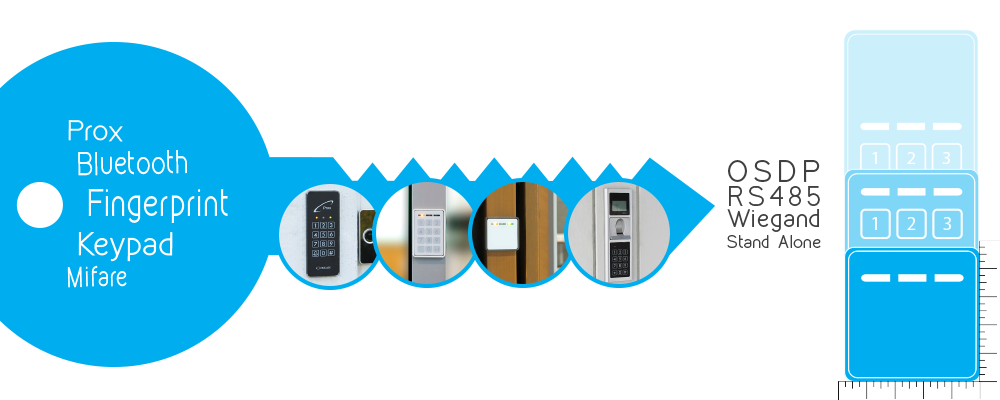
Reader Technology
How to open your door
Pin Code
Get rid of keys and cards and open the door using your own personal pin code. With a capacitive touch keypad, you get maximum comfort and durability. The keypad responds to the energy of your finger and does not deteriorate, as there are no moving parts under the keys.
In addition to your personal pin, you may use 24 hour pins or single use pins, if you need to provide access for a shorter period of time.
Read more about 24 hour pins and single use pins.
Bluetooth
Why not open your door with the one thing that you always keep with you – your phone? Our Bluetooth readers recognise standard Bluetooth as well as low energy Bluetooth/smart Bluetooth.
Proximity
In many ways, proximity access control works the same way as a regular key – you need a transponder or card to access. However, a few important advantages distinguish proximity access control from a mechanical lock:
New transponder types a much more difficult to copy, than mechanical keys.
- You can edit users and disable access, even if the user does not return the transponder or card.
- You can keep a log of who entered the building and when.
Our proximity readers read Atmel, Emarine, Mifare and DESfire.
Mifare/DESfire
Using the new proximity signals lets you use a single card for multiple purposes. A Mifare card has the ability to store many layers of information such as access privileges, licenses and certificates, and you can even use it for payment purposes.
Combinations
Reader technologies may be combined for two reasons:
- To increase security by demanding two types of reading before access is granted. You may wish to require both pin and proximity reading. This may be required at all times or within a certain time frame, e.g. at night.
- As a backup if your primary reader technology is unavailable. For instance, we recommend installing a backup technology with our Bluetooth readers, in case your phone runs out of battery.
There are many possibilities and you are welcome to contact us with any inquiries you may have.
Get an overview of the possibilities in our product portfolio.
Reader Communication
Communication between Reader and Controller
Stand Alone
Stand Alone systems are our specialty. In brief, Stand Alone means that you do not need a pc to install or program your access control. As such, Stand Alone is the logical solution for most small installations.
Programming
All programming, editing and termination of users is done on the reader. You may have several installations with the same pins, transponders, fingers etc. and you may connect your access control to your alarm system as well. If you need to program several readers with the same information, you can program just one and then transfer the information to the remaining readers.
Read more about cloning of readers.
Logging
If you want to log who accessed your property and when, you should apply our log box. When you need to read the log simply detach the log box from the access control reader and connect it to your pc, where a small software program will display the last 10.000 logs.
Wiegand
Readers with Wiegand output may be set at 4-58 bit. Perfect for integration with Wiegand controllers and systems employing an approved Wiegand protocol.
OSDP
Open Supervised Device Protocol is a new standard of open source communication. OSDP comes in an incrypted version and an open version.
RS485 Open Protocol
RS485 and RS485 open collector communication may be integrated with other installations and controllers. Front end software included.